
Do you drink water? Do you take showers? Have you turned the lights on in your house? Chances are you’ve indirectly touched an industrial control system. Industrial control systems power our daily lives, and these systems must be protected from cyber-attacks. Over the past 10 years, I’ve been fortunate to bear witness to the increased complexity of control systems and the ever-evolving nature of Industrial Automation Control Systems (IACS). As part of the industrial automation community, I wanted to share with you a few cybersecurity resources that I’ve employed over the years as a contribution to strengthening industrial cybersecurity awareness, education, and resilience.
Control System Modernization

As time passes programmable logic controllers, remote terminal units, intelligent electronic devices, and SCADA systems are continuing to modernize, evolve, and adapt. Many of today’s modern devices and software are delivered with the ability to connect to the internet via various technologies i.e. ethernet ports, embedded webservers, and wireless functionality. These common examples aide in widespread internet connectivity and allow for greater transparency and cost savings. However, they also increase cybersecurity risks.
“It is not an if, it is a when statement.”
-Cybersecurity Community
What is the Cybersecurity Threat?
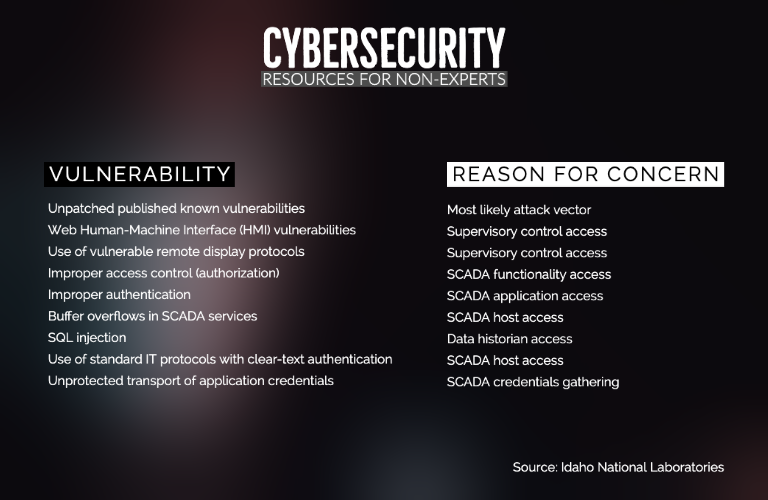
I have heard this comment time and time again amongst the cybersecurity community with good reason. According to Business Advantage State of Industrial Cybersecurity (2017), 54% of companies experienced an industrial control system security incident within the past 12 months, and 16% had experienced three or more. All an attacker needs to compromise a system is one access point. Even if your system is completely disconnected from the internet, attackers can gain access to your local area network and wreak havoc in a number of different ways. The following list of common vulnerabilities was compiled by Idaho National Laboratories. These vulnerabilities were routinely discovered during testing at their National SCADA Test Bed.
Understanding and having an awareness of the threat is the first step and the beginning of educating yourself on how to protect your IACS system. Where do we go from here?
Cybersecurity Action Driven by Regulation
I still to this day see common vulnerabilities every time I am on a customer’s site. Simple things like SCADA servers not under lock and key, unmanned HMI terminals that are logged into, and generic username/passwords (operator/operator). The threat is very real, just google search “ICS attack” to see any number of attacks on major industrial automation control systems. Recently, the threat hit home with the WannaCry ransomware virus taking one of our automotive customer’s production factories offline. For years cybersecurity has been talked about in our industry and it never really seemed to drive action, however, with cyber-attacks growing at an exponential rate, there have been two key events that I’ve taken mental note of because I believe they are going to drive cybersecurity change through regulation.
Department of Homeland Security Executive Order

This is directly from the DHS website. In May 2009, President Obama declared our digital infrastructure a strategic national asset, recognizing that protecting the networks and computers that deliver essential services such as our oil and gas, power, and water is a national security priority. President Obama is committed to doing everything in his power to protect these systems from cyber-threats. In May 2011, the Obama Administration sent Congress a cybersecurity legislative proposal. Today the President signed an Executive Order (EO) on Cybersecurity and a Presidential Policy Directive (PPD) on Critical Infrastructure Security and Resilience. These actions will strengthen the security and resilience of critical infrastructure against evolving threats through an updated and overarching national framework that acknowledges the increased role of cybersecurity in securing physical assets.
Learn more about the Department of Homeland Security Executive Order of 2009
State-Mandated Cybersecurity Requirements
Our industry has a track record of being “behind the times”, however, to my surprise in 2016 the New Jersey Board of Public Utilities created, to the best of my knowledge, the first state-mandated Utility Cybersecurity Program requirements. This excerpt is from the State of New Jersey:
“The New Jersey Board of Public Utilities (“Board”) initiated this matter in order to establish requirements to mitigate cyber risks to critical systems of electric, natural gas, and water/wastewater utilities (“Utilities”). As technology advances, Utilities’ computerized systems are increasingly susceptible to cybersecurity attacks, including data breaches, corporate theft, and sabotage perpetrated by actors throughout the world. Due to the critical nature of the Utilities’ services, the Board recognizes that action is necessary to mitigate cybersecurity risks to Utilities’ computerized systems. In addition, to the extent information is shared and provided by the Utilities; the Board recognizes that such information is confidential and sensitive and requires appropriate confidentiality protections.”
With the US government creating critical infrastructure oversight, it is just a matter of time before IACS systems need to adhere to fully adopted state and federal cybersecurity regulations.
Learn more about the State of New Jersey Board of Public Utilities
How long until cybersecurity regulation is adopted by other utility districts? Could this regulation be the cybersecurity trend to drive vendors to improve their products, IT managers to become more familiar with IACS, and OT systems engineers to comply with cybersecurity requirements? Only time will tell, but in the meantime, you can prepare yourself for a future that sees no end in sight to cybersecurity threats.
Getting Started with Cybersecurity Standards
First and foremost, if you are an industrial automation control systems professional, utilizing cybersecurity standards for system deployment and maintenance is beneficial. Both the industrial and commercial markets have established cybersecurity groups with focused committees that organize best practices and standards. There are two authorities worth noting that I recommend familiarizing yourself with. The first is the National Institute of Standards and Framework (NIST). The NIST Cybersecurity Framework is now used by 30 percent of U.S. organizations, according to the information technology research company Gartner and they are considered the cybersecurity authority.
NIST standard 800-82 is where you can find Industrial Automation Control System information. This particular standard has branched off and is mirrored by ISA/IEC 62443 (Formerly ISA 99), which is the second cybersecurity resource worth noting. Information Technology (IT) professionals are typically more familiar with NIST and Operations Technology professionals (OT) typically reference ISA/IEC 62443 industrial automation control system cybersecurity standards. Both NIST and ISA/IEC 62443 are valuable resources to leverage. Here is an ISA/IEC 62443 graphical reference model that depicts the status of the work in progress cybersecurity standard.

Learn more about ISA/IEC 62443
Free Virtual Training
If you are part of an IACS operations team, IT professional, or OT professional there is a fantastic virtual learning program provided by Idaho National Laboratories and available for free. This free virtual learning covers a range of cybersecurity topics from operational security to defense in depth. The content is accredited by the International Association for Continuing Education and Training (IACET) and is accredited to issue IACET Continuing Education Units (CEUs).
Learn more about Cybersecurity + Infrastructure Security Association (CISA) virtual training
Zero-Day Documentary
If you’re into documentaries, I highly suggest Zero-Day. It focuses on the self-replicating malware Stuxnet and is both insightful and entertaining.
Check out Zero-Day Documentary
At a glance, I hope these resources help improve your overall cybersecurity awareness and knowledge. What cybersecurity resources do you use? Please share them with us in the comment section below.